Chisel - SOCKS5 Tunneling - Linux
Setting Up
Before we can use Chisel, we need to have it on our attack host git clone. We will need the programming language Go installed on our system to build the Chisel binary. With Go installed on the system, we can move into that directory and use go build to build the Chisel binary.
git clone on Attack Host
Building the Chisel Binary on Attack Host
Transferring Chisel Binary to Pivot Host
Using Chisel
SSH to Pivot Host
Then we can start the Chisel server/listener on Pivot Host./chisel.elf server -v -p 1234 --socks5
|->
2023/04/13 06:50:57 server: Fingerprint eRCF9nVnkRmX3/+CZrMEiGmkDL1LZJAvgzmlOTL4z8A=
2023/04/13 06:50:57 server: Listening on http://0.0.0.0:1234
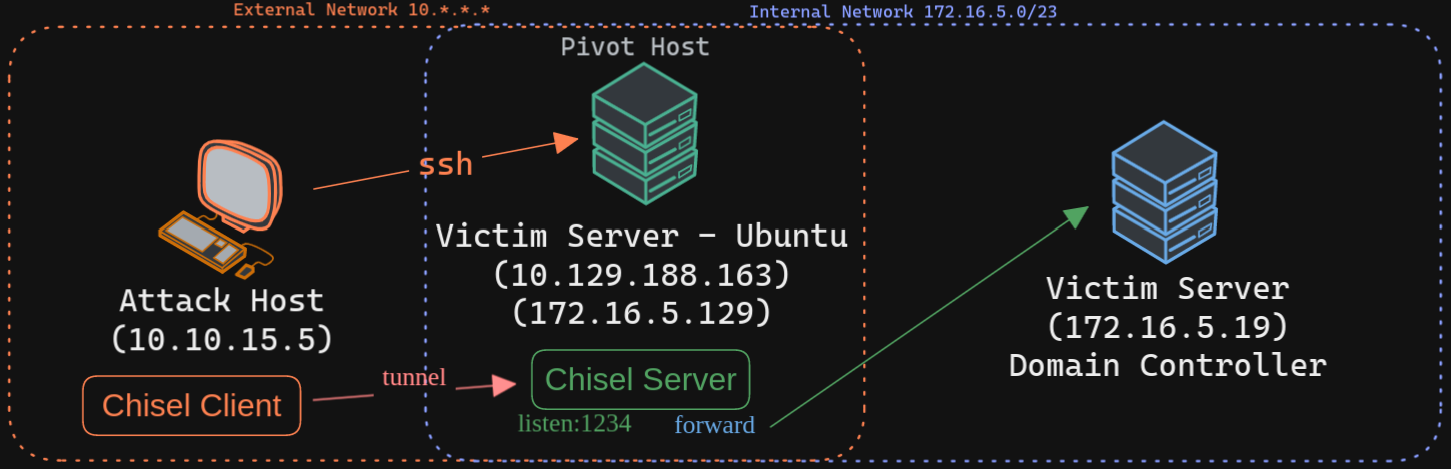
The Chisel listener will listen for incoming connections on port 1234 using SOCKS5 (--socks5) and forward it to all the networks that are accessible from the pivot host. In our case, the pivot host has an interface on the 172.16.5.0/23 network, which will allow us to reach hosts on that network.
We can start a client on our attack host and connect to the Chisel server.
./chisel.elf client -v 10.129.188.163:1234 socks
|->
2023/04/13 02:51:20 client: Connecting to ws://10.129.188.163:1234
2023/04/13 02:51:20 client: tun: proxy#127.0.0.1:1080=>socks: Listening
2023/04/13 02:51:20 client: tun: Bound proxies
2023/04/13 02:51:20 client: Handshaking...
2023/04/13 02:51:20 client: Sending config
2023/04/13 02:51:20 client: Connected (Latency 59.238383ms)
2023/04/13 02:51:20 client: tun: SSH connected
Editing & Confirming proxychains.conf As you can see in the above output, the Chisel client has created a TCP/UDP tunnel via HTTP secured using SSH between the Chisel server and the client and has started listening on port 1080. Now we can modify our proxychains.conf file located at /etc/proxychains.conf and add 1080 port at the end so we can use proxychains to pivot using the created tunnel between the 1080 port and the SSH tunnel. We can use any text editor we would like to edit the proxychains.conf file, then confirm our configuration changes using tail.
tail -n2 /etc/proxychains4.conf # or proxychains.conf
|->
# socks4 127.0.0.1 9050
socks5 127.0.0.1 1080
Pivoting to the DC
Addon - Chisel Reverse Pivot
In the previous example, we used the compromised machine (Ubuntu) as our Chisel server, listing on port 1234. Still, there may be scenarios where firewall rules restrict inbound connections to our compromised target. In such cases, we can use Chisel with the reverse option. When the Chisel server has --reverse enabled, remotes can be prefixed with R to denote reversed. The server will listen and accept connections, and they will be proxied through the client, which specified the remote. Reverse remotes specifying R:socks will listen on the server's default socks port (1080) and terminate the connection at the client's internal SOCKS5 proxy.
Starting the Chisel Server on our Attack Host
Then we connect from the Ubuntu (pivot host) to our attack host, using the option R:socks
Editing & Confirming proxychains.conf
If we use proxychains with RDP, we can connect to the DC on the internal network through the tunnel we have created to the Pivot host.
Appendix
In case of error
./chisel: /lib/x86_64-linux-gnu/libc.so.6: version `GLIBC_2.32' not found (required by ./chisel)
./chisel: /lib/x86_64-linux-gnu/libc.so.6: version `GLIBC_2.34' not found (required by ./chisel)
use older version of chisel -> https://github.com/jpillora/chisel/releases/tag/v1.7.4